Make Best Use Of Effectiveness with LinkDaddy Cloud Services Press Release Insights
Make Best Use Of Effectiveness with LinkDaddy Cloud Services Press Release Insights
Blog Article
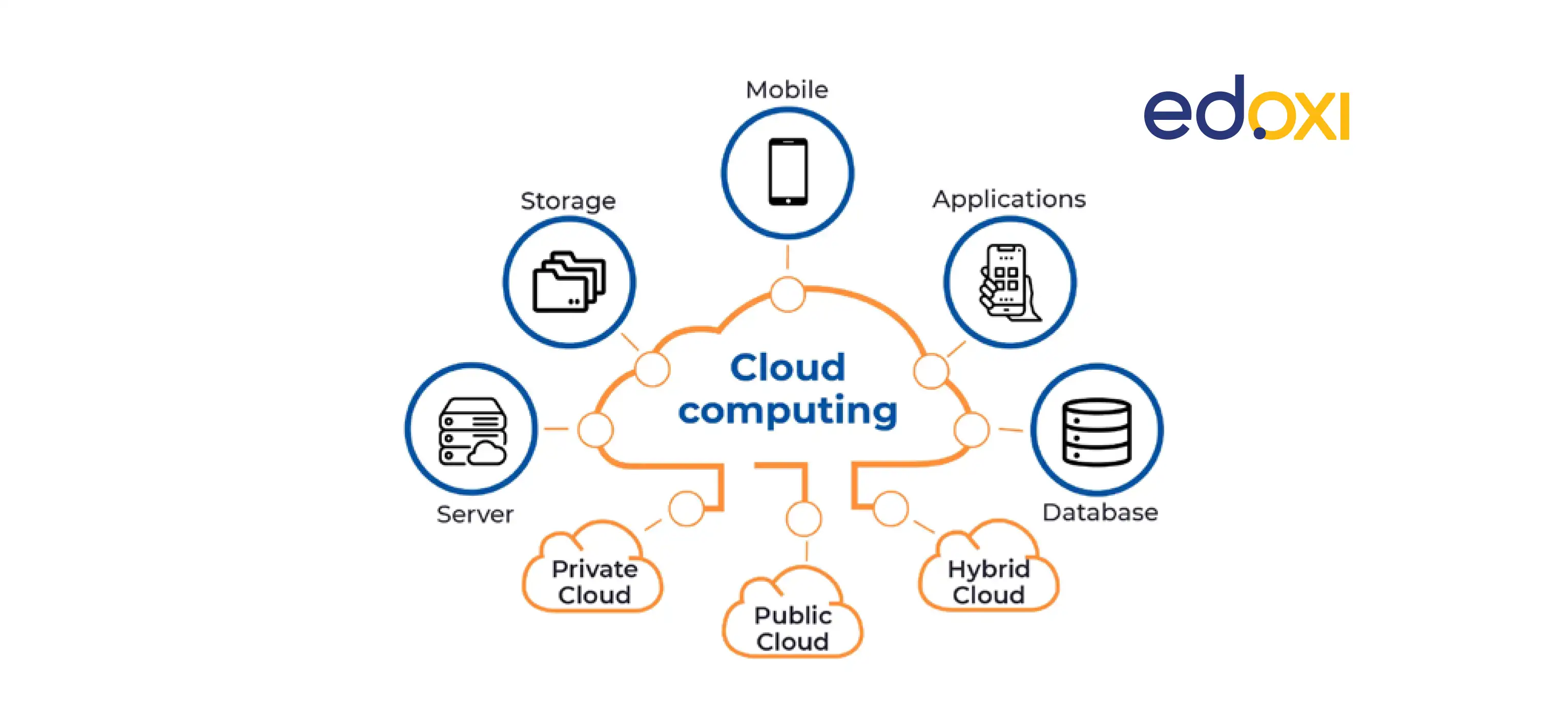
Secure and Efficient: Maximizing Cloud Providers Advantage
In the fast-evolving landscape of cloud services, the crossway of security and effectiveness stands as a critical time for companies seeking to harness the full capacity of cloud computing. By diligently crafting a framework that focuses on information protection through file encryption and gain access to control, companies can fortify their electronic properties against impending cyber dangers. The mission for ideal efficiency does not end there. The equilibrium between securing information and guaranteeing structured procedures needs a strategic technique that requires a deeper exploration into the elaborate layers of cloud service monitoring.
Information File Encryption Ideal Practices
When executing cloud solutions, utilizing durable data security finest methods is paramount to protect delicate details efficiently. Information file encryption entails inscribing details as though just authorized events can access it, ensuring privacy and safety and security. One of the essential ideal techniques is to use strong encryption algorithms, such as AES (Advanced Encryption Criterion) with secrets of ample length to shield information both in transit and at remainder.
Additionally, executing correct key management strategies is vital to maintain the security of encrypted information. This includes firmly producing, storing, and revolving encryption keys to avoid unapproved gain access to. It is likewise important to secure data not only during storage yet likewise during transmission between individuals and the cloud provider to stop interception by malicious actors.
Source Allowance Optimization
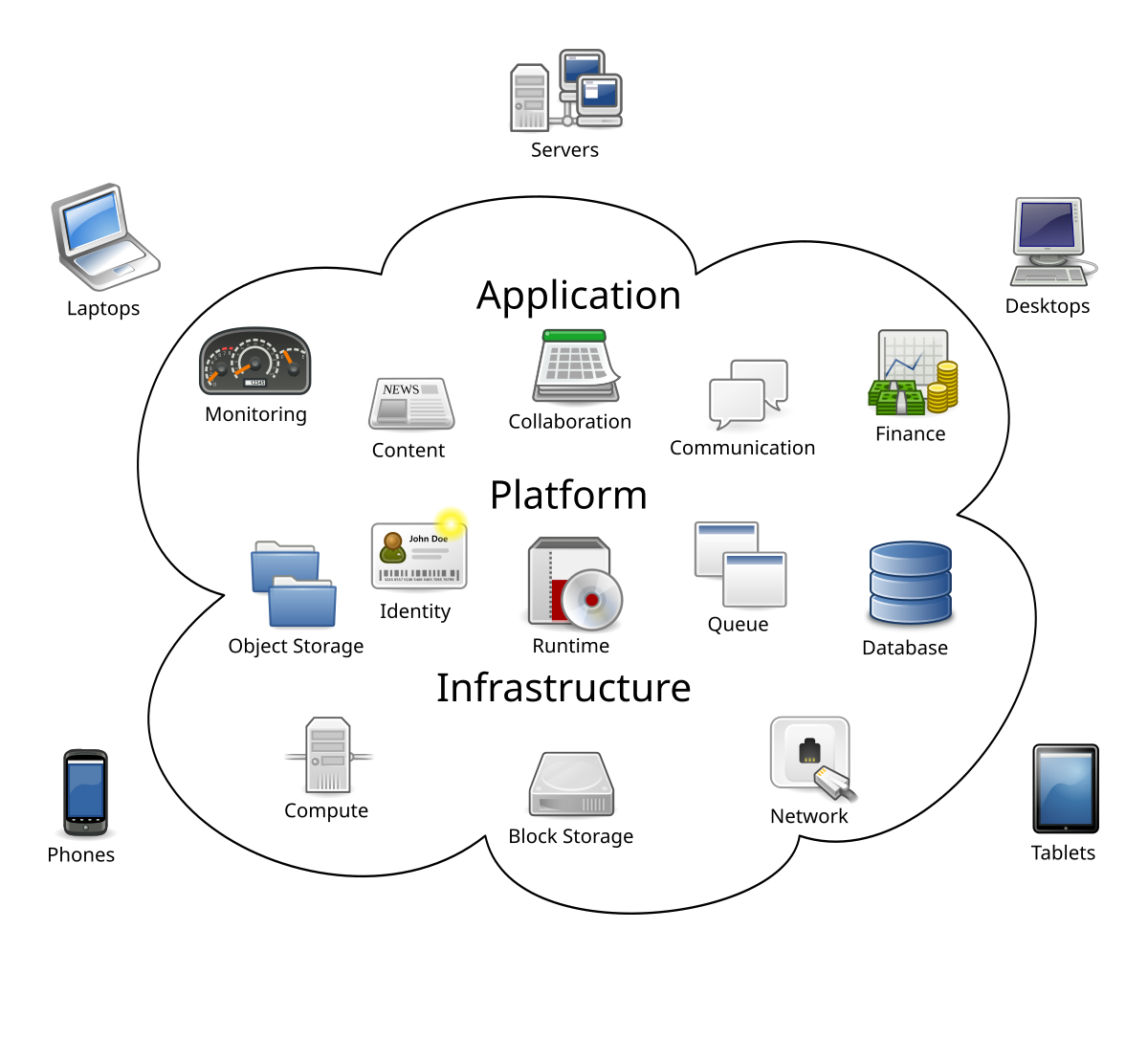
To take full advantage of the advantages of cloud services, companies have to concentrate on optimizing source allowance for efficient procedures and cost-effectiveness. Resource allowance optimization involves purposefully distributing computer resources such as refining power, network, and storage space transmission capacity to satisfy the varying demands of work and applications. By carrying out automated resource allotment systems, organizations can dynamically adjust source circulation based upon real-time needs, ensuring optimal efficiency without unneeded under or over-provisioning.
Effective source allowance optimization results in enhanced scalability, as resources can be scaled up or down based on use patterns, causing boosted flexibility and responsiveness to altering organization needs. By properly lining up resources with workload needs, companies can lower operational prices by removing waste and maximizing usage performance. This optimization additionally improves total system integrity and resilience by stopping source bottlenecks and making sure that important applications receive the required sources to work smoothly. Finally, resource allocation optimization is necessary for companies seeking to take advantage of cloud services effectively and securely.
Multi-factor Authentication Application
Carrying out multi-factor authentication boosts the safety position of organizations by needing extra confirmation steps past simply a password. This added layer of safety and security significantly reduces the threat of unauthorized access to delicate data and systems. Multi-factor verification typically integrates something the individual knows (like a password) with something they have (such as a smart phone) or something they are (like a Continued finger print) By including several elements, the likelihood of a cybercriminal bypassing the authentication process is greatly lessened.
Organizations can pick from numerous methods of multi-factor authentication, including SMS codes, biometric scans, equipment tokens, or authentication applications. Each approach provides its own level of safety and ease, permitting companies to pick the most ideal alternative based on their special needs and resources.
Furthermore, multi-factor verification is crucial in safeguarding remote access to cloud solutions. With the boosting trend of remote job, making certain that only authorized employees can access important systems and information is vital. By applying multi-factor verification, companies can fortify their defenses against potential safety and security violations and information burglary.
Disaster Recuperation Planning Methods
In today's electronic landscape, reliable disaster healing preparation techniques are crucial for organizations to alleviate the effect of unanticipated disturbances on their information and procedures honesty. A robust disaster healing plan involves recognizing potential risks, analyzing their possible influence, and applying aggressive steps to guarantee organization continuity. One crucial facet of calamity healing planning is developing backups of important information and systems, both on-site and in the cloud, to make it possible for swift remediation in case of an incident.
Additionally, organizations should carry out normal testing and simulations of their disaster recuperation treatments to determine any kind of weaknesses and enhance response times. Furthermore, leveraging cloud services for catastrophe recovery can offer cost-efficiency, scalability, and versatility compared to traditional on-premises solutions.
Performance Keeping An Eye On Tools
Performance tracking devices play an important duty in offering real-time understandings into the health and wellness and effectiveness of an organization's systems and applications. These click site tools enable services to track different performance metrics, such as feedback times, source usage, and throughput, enabling them to identify bottlenecks or potential concerns proactively. By constantly keeping track of key performance indicators, companies can ensure optimum performance, identify fads, and make educated choices to enhance you could try these out their total operational performance.
One popular performance tracking tool is Nagios, understood for its ability to monitor servers, networks, and solutions. It gives comprehensive tracking and notifying solutions, ensuring that any kind of deviations from set efficiency thresholds are swiftly determined and addressed. One more commonly utilized device is Zabbix, supplying monitoring capabilities for networks, web servers, virtual makers, and cloud solutions. Zabbix's easy to use interface and customizable functions make it a useful possession for organizations seeking durable efficiency tracking solutions.
Verdict
In the fast-evolving landscape of cloud services, the crossway of security and efficiency stands as an essential juncture for organizations looking for to harness the full capacity of cloud computing. The balance between securing information and making sure structured operations requires a tactical method that necessitates a deeper expedition right into the detailed layers of cloud solution management.
When implementing cloud services, using durable information security best techniques is paramount to protect sensitive information successfully.To maximize the benefits of cloud solutions, companies have to concentrate on enhancing source allotment for effective procedures and cost-effectiveness - cloud services press release. In verdict, resource allotment optimization is necessary for companies looking to leverage cloud services efficiently and securely
Report this page